 In the past, the vast majority of large mechanical and process piping systems in power plants, manufacturing facilities and wastewater plants were isolated and “dumb.” Even computerized systems employed proprietary operating protocols. In essence, this kept the equipment isolated or “air-gapped” from the outside world. Over time, the growing demand for enhanced resource utilization and lower operating costs forced administrators to modernize by connecting indirectly or directly to the internet. While the benefits in terms of efficiency and productivity have been extraordinary, industrial control systems are now subject to the same vulnerabilities traditionally reserved for enterprise-level IT systems.
In the past, the vast majority of large mechanical and process piping systems in power plants, manufacturing facilities and wastewater plants were isolated and “dumb.” Even computerized systems employed proprietary operating protocols. In essence, this kept the equipment isolated or “air-gapped” from the outside world. Over time, the growing demand for enhanced resource utilization and lower operating costs forced administrators to modernize by connecting indirectly or directly to the internet. While the benefits in terms of efficiency and productivity have been extraordinary, industrial control systems are now subject to the same vulnerabilities traditionally reserved for enterprise-level IT systems.
Targeted Attacks Against ICSs
International thieves, terrorists and unscrupulous competitors pose a serious threat to ICSs throughout the world. This is due to the emergence of the Internet of Things (IoT) and Industrial IoT as well as the increased use of remote telemetry for monitoring and input. These relatively recent developments provide hackers with numerous entry points for nefarious activities that can negatively affect the operational efficacy of critical process systems along with the health, safety and financial security of people and companies worldwide.
The most famous ICS attack occurred in 1982 when the CIA used malware to infect SCADA software the Soviet Union had stolen to control a Siberian pipeline. [1] Ultimately, the software began closing safety valves until the pressure became so great that welds and joints failed, and the entire pipeline exploded.
In the past 25 years, there has been a significant rise in reported cyber-attacks. This is due to the availability of resources and hackers’ superior knowledge. Advanced persistent threats (APT) incorporate advanced tools with coordinated human participation to initiate and control an attack using one or more control centers. Attackers strive to keep the incursion hidden so they can complete the mission while remaining undetected. In most instances, there is very little forensic evidence left behind.
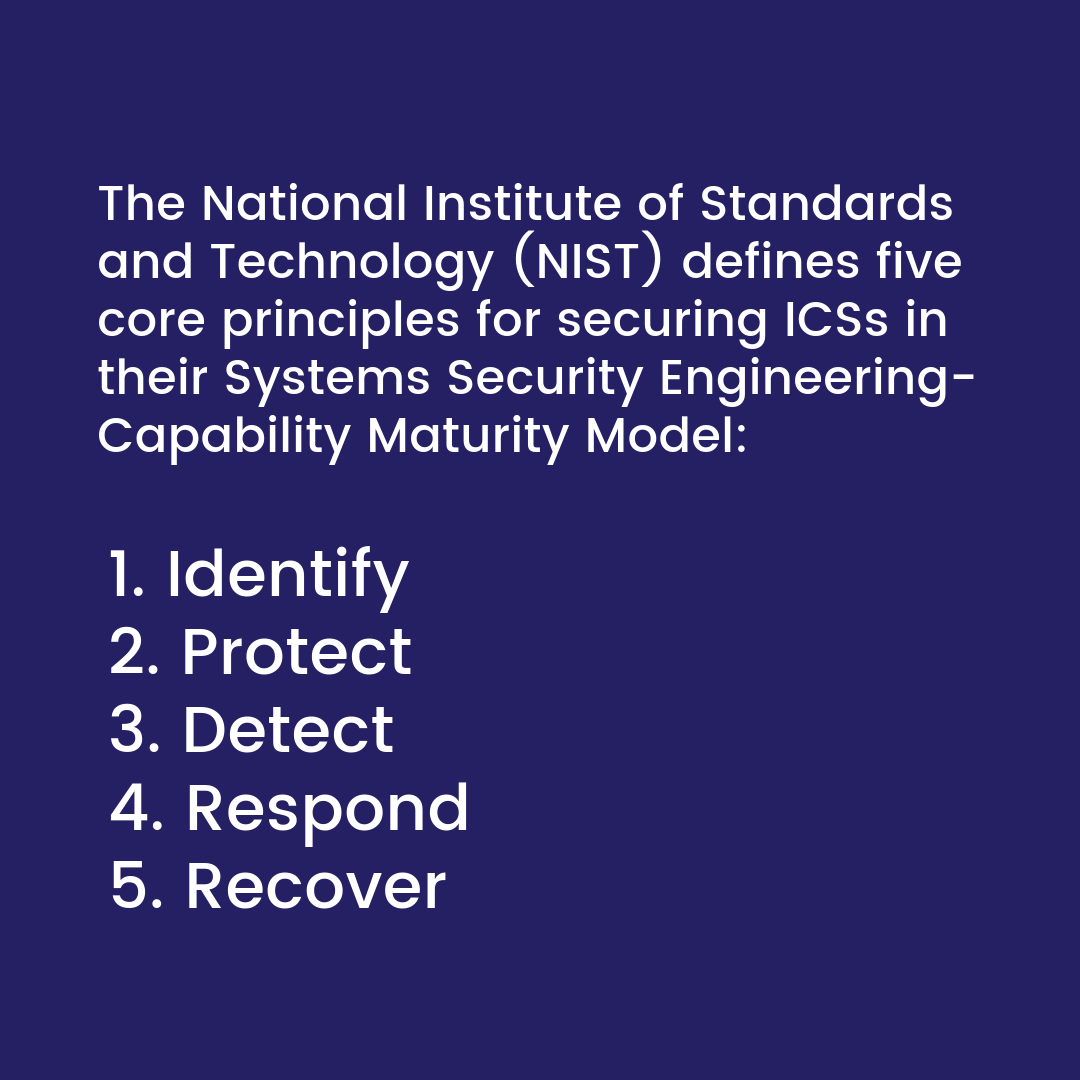 The National Institute of Standards and Technology (NIST) defines five core principles for securing ICSs in their Systems Security Engineering-Capability Maturity Model: [2]
The National Institute of Standards and Technology (NIST) defines five core principles for securing ICSs in their Systems Security Engineering-Capability Maturity Model: [2]
- Identify: The process of developing an understanding within the organization on how to manage cybersecurity risk relating to assets, data, people, systems and capabilities.
- Protect: The development and implementation of standards and safeguards to ensure the delivery of critical services. This includes, Information Protection Processes and Procedures, Identity Management and Access Control, Maintenance and Protective Technology and Awareness Training and Data Security.
- Detect: The development and implementation of activities and techniques designed to identify and expose a cybersecurity event.
- Respond: The subsequent action and activities intended to contain the impact of a detected cybersecurity event.
- Recover: Develop appropriate activities to restore or replace services impaired by a cybersecurity incident.
The Important Role of Industrial Control Systems Firewalls
Unfortunately, studies indicate that up to 96 percent of local Industrial Control System traffic is currently unprotected. [3] Firewalls play an important role in maintaining the integrity of any network, and ICS is no different. A firewall serves as a filter to differentiate between desired traffic and potential threats. ICS networks are typically segmented to provide a broad defense-in-depth strategy. Firewall implementation is usually based on the Purdue Model, which divides networks into six levels. [4]
- Level 5: The enterprise layer is where the corporate office and network operate.
- Level 4: This is also an enterprise level but serves branch offices and the locations where the equipment is installed.
- Level 3: This is the level where SCADA systems reside so they can be accessed by enterprise entities and also communicate with components on lower levels
- Level 2: The Area Supervisory Control where components like PLCs and HMIs reside.
- Level 1: This is where the majority of PLCs are located and where control of the OT (operational technology) takes place.
- Level 0: This is the OT equipment.
 Don’t Compromise on ICS Security
Don’t Compromise on ICS Security
While firewalls are the backbone of an effective ICS protection strategy, it’s important to remember that they can only defend against attacks initiated outside the network. To combat malware introduced from USB devices and other control network components, the control system must also incorporate host-based protection operating on the inside of the system in order to compliment the firewall’s perimeter protection. Therma has extensive experience installing, repairing and protecting critical ICS systems, and they can implement a host of comprehensive defensive measures to ensure your equipment and control systems continue to operate safely, economically and without disruption.
By William Busse
William Busse has more than 30 years experience in the construction industry in sales, contracting, distribution and manufacturing. He has an extensive background in the mechanical contracting industry, largely from the distribution and manufacturing sides of the business. He has had deep involvement with a variety of large-scale commercial/industrial mechanical contractors, particularly related to value engineering. This includes process piping, high-pressure steam, cryogenics, thermal insulation and commercial/industrial HVAC.
Sources
- https://www.telegraph.co.uk/news/worldnews/northamerica/usa/1455559/CIA-plot-led-to-huge-blast-in-Siberian-gas-pipeline.html
- https://nvlpubs.nist.gov/nistpubs/CSWP/NIST.CSWP.04162018.pdf
- https://www.technologyreview.com/s/612829/industrial-control-systems-are-still-vulnerable-to-malicious-cyberattacks/
- http://citeseerx.ist.psu.edu/viewdoc/download?doi=10.1.1.194.6112&rep=rep1&type=pdf
- https://www.osti.gov/servlets/purl/1376870
- https://ws680.nist.gov/publication/get_pdf.cfm?pub_id=821684